The Trust Triad: How Agentic AI, Pindrop, and Anonybit Redefine Enterprise Security 2026
Table of Contents
Imagine it is 3:00 AM. Your phone vibrates on the nightstand—not with a standard notification, but with a high-priority alert from your Security Operations Center (SOC). A high-value wire transfer was just initiated by your CFO. The voice on the recorded line was perfect. The credentials used were valid. Every traditional check-box was ticked.
Yet, your system flagged it as a fraud.
Why? Because your enterprise has moved beyond the “castle and moat” era of security. You are no longer just reacting to threats; you are anticipating them through a sophisticated, autonomous ecosystem. This is the reality of the Trust Triad. By weaving together Agentic AI, Pindrop, and Anonybit, you aren’t just building a bigger wall; you are creating a digital immune system that understands liveness, decentralizes identity, and acts with the speed of thought.
In this deep dive, we will explore how these three revolutionary technologies converge to solve the most pressing crisis in modern business: the total collapse of traditional trust.
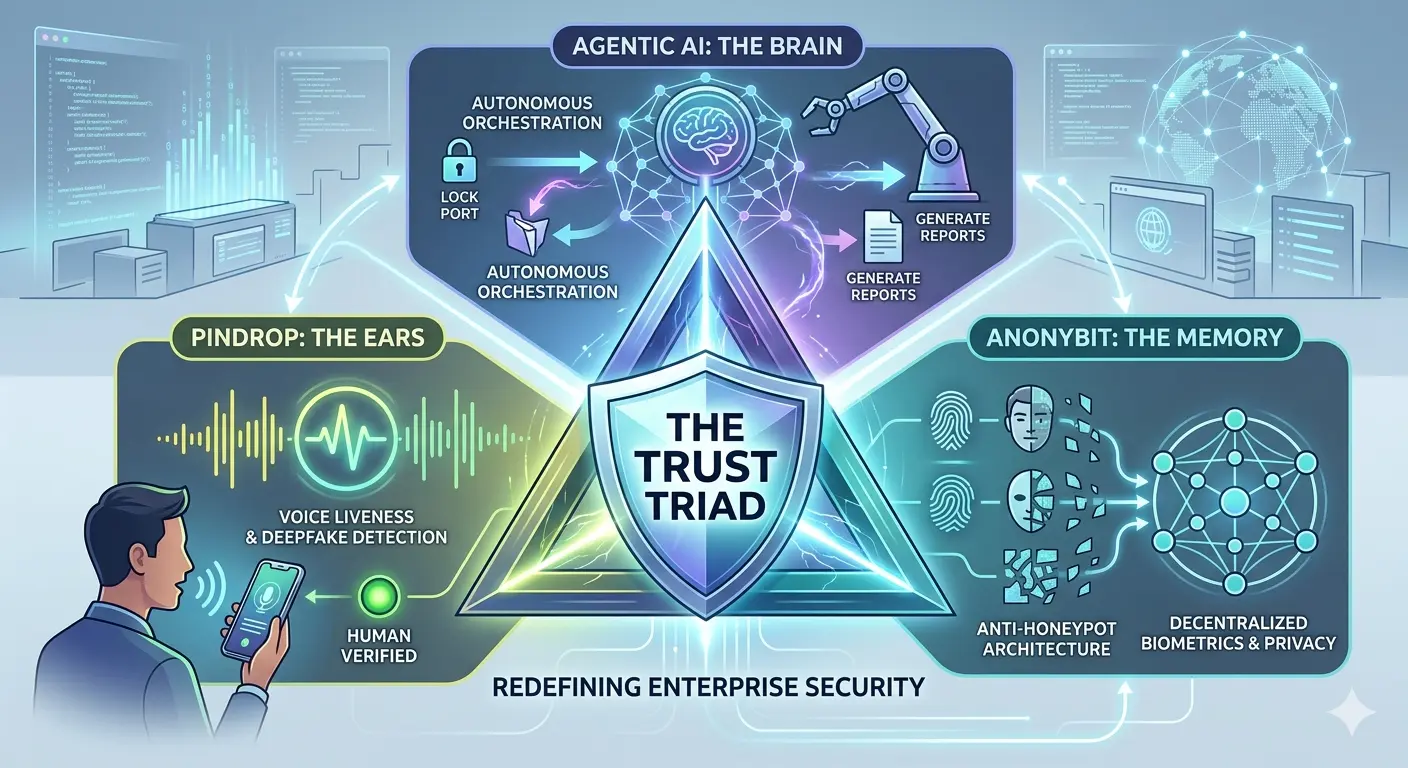
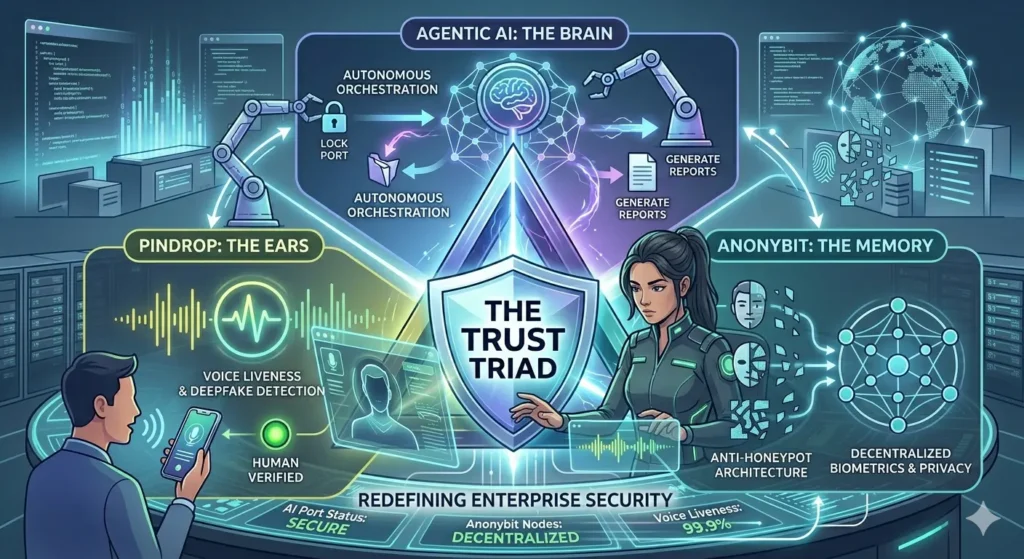
Defining the Players: Who is the Trust Triad?
To understand how you can protect your organization in a world dominated by generative AI threats, you first need to understand the three pillars of modern defense. Each addresses a specific failure point in the legacy security stack.
Agentic AI: The “Brain” of the Operation
You’ve likely interacted with LLMs (Large Language Models) that answer questions. Agentic AI is different. It doesn’t just “know” things; it “does” things. It has agency. In your security architecture, Agentic AI acts as the connective tissue. It perceives an environment, reasons through a problem, and executes a multi-step plan to resolve it. Think of it as a senior security engineer that lives inside your network, capable of closing ports, revoking tokens, and investigating anomalies in milliseconds.
Pindrop: The “Ears” that Never Lie
As deepfake audio becomes indistinguishable from human speech to the naked ear, your call centers and remote authentication protocols are under siege. Pindrop provides the solution through voice liveness detection. It doesn’t listen to the words spoken; it analyzes the physics of the sound. By identifying the tell-tale signs of synthetic audio or digital playback, Pindrop ensures that when you hear a “person” on the other end, they are actually made of flesh and blood.
Anonybit: The “Memory” without a Target
The biggest vulnerability in your company is likely your biometric database. If you store thousands of faces or fingerprints in one central server, you’ve created a “honeypot” for hackers. Anonybit changes this by decentralizing identity. It takes a biometric template, breaks it into encrypted fragments, and scatters them across a decentralized cloud. There is no central record to steal, making your users’ identities virtually unhackable.
How Agentic AI, Pindrop, and Anonybit Work Together
When you integrate these three, you transition from a reactive posture to a proactive orchestration. Let’s look at how this triad manages a high-stakes authentication event in real-time.
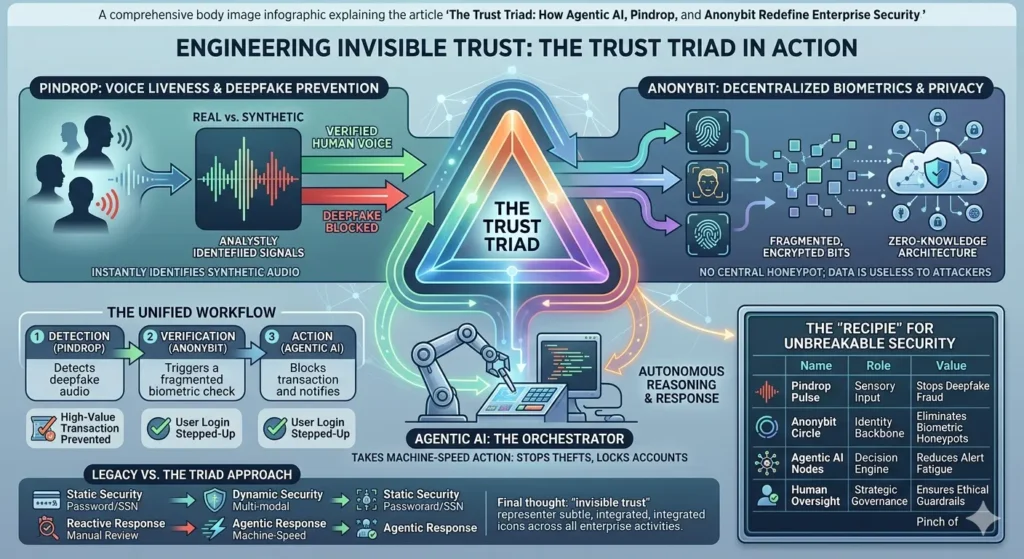
The Unified Workflow
- Detection: A user attempts to access a restricted terminal via voice command. Pindrop immediately analyzes the audio stream for “liveness.”
- Verification: Simultaneously, the system requests a biometric “proof.” Anonybit retrieves encrypted fragments from across the network to verify the user without ever reconstructing the full biometric image in a single location.
- Action: The Agentic AI monitors this interaction. If Pindrop flags a 10% chance of synthetic audio, the AI doesn’t wait for a human. It autonomously decides to “step up” the authentication, perhaps requiring a hardware-based security key or a secondary biometric check, and alerts the SOC.
Comparative Analysis of Security Layers
To see why you need this triad, look at how it compares to the legacy systems you might still be running.
| Security Component | Traditional Approach | The Trust Triad (Agentic AI, Pindrop, Anonybit) |
| Authentication Source | Static Passwords/SSN | Dynamic Voice Liveness & Decentralized Biometrics |
| Threat Response | Manual/Rule-based | Autonomous/Agentic Reasoning |
| Storage Risk | Centralized Honeypots | Fragmented & Anonymous |
| Deepfake Defense | None (Human judgment) | Algorithmic Liveness Detection |
| Scalability | High overhead for SOC | Machine-speed automation |
Solving the “Honeypot” Problem with Anonybit
You have probably spent millions of dollars securing your data, but have you considered the liability of your biometric storage? Under regulations like GDPR and CCPA, a breach of biometric data isn’t just a technical failure; it’s a legal catastrophe.
Anonybit allows you to adopt a “Zero-Knowledge” architecture. When you use Anonybit, you aren’t actually “storing” biometrics. You are storing mathematical representations that are useless on their own. This removes the incentive for attackers. If there is no central vault to crack, the “Return on Investment” for a hacker drops to zero. You are effectively making your enterprise an “identity-empty” target while maintaining the highest levels of user verification.
Countering Deepfakes with Pindrop Pulse
If you think your team can spot a deepfake, you are already behind. Modern “speech-to-speech” models can mimic tone, breathing patterns, and emotional inflection with 99% accuracy. Your contact centers are the front line of this war.
By implementing Pindrop, you provide your frontline staff with a “trust score” for every call. Pindrop Pulse detects:
- Synthetic Speech: Audio generated by AI models.
- Replay Attacks: Recorded voices played back through a device.
- Voice Clones: AI-generated replicas of specific individuals.
This isn’t just about security; it’s about customer experience. When you trust the voice, you can reduce those annoying “security questions” that frustrate your genuine clients, streamlining your operations while tightening the net for fraudsters.
The Rise of Agentic AI as the Enterprise Orchestrator
The “secret sauce” that makes this triad work is the Agentic AI. For years, we’ve had AI that flags alerts—and then sits there waiting for a human to click “Approve” or “Deny.” That delay is where the damage happens.
Agentic AI acts as the “General” on the digital battlefield. It uses the data from Pindrop and Anonybit to make contextual decisions. For instance, if a user is verified via Anonybit but Pindrop detects high background noise consistent with a “fraud farm” environment, the Agentic AI can choose to limit the user’s transaction limit to $500 until a human can review the case. You are moving from a binary “Yes/No” security model to a nuanced, risk-weighted model that operates at the speed of the internet.
H3: The Recipe for an Unbreakable Security Stack
To implement this in your organization, think of it as a recipe where the quality of the ingredients determines the safety of the outcome.
| Ingredient | Role in the Triad | Value to the Enterprise |
| Pindrop Pulse | Sensory Input | Eliminates “Identity Theft by Voice” and deepfake fraud. |
| Anonybit Circle | Identity Backbone | Removes the liability of biometric data storage. |
| Agentic AI Nodes | Decision Engine | Automates response, reducing “Alert Fatigue” for your team. |
| Zero Trust Policy | Governance | Ensures no user is trusted by default, regardless of rank. |
Frequently Asked Questions (FAQ)
How do Agentic AI, Pindrop, and Anonybit protect against insider threats?
While Pindrop and Anonybit verify the “who,” Agentic AI monitors the “what.” Even if an insider is authenticated, the Agentic AI tracks their behavior. If a trusted employee suddenly starts downloading the entire client database at 2:00 AM, the AI recognizes the anomaly and revokes access instantly.
Is this Triad difficult to integrate with legacy IAM systems?
No. Most modern enterprises use this triad as an “augmentation layer.” You don’t have to rip and replace your existing Identity and Access Management (IAM) stack. Anonybit and Pindrop plug into your existing flows via APIs, while Agentic AI sits on top as the orchestrator.
Does decentralized biometric storage affect the speed of login?
Surprisingly, it can be faster. Because Anonybit uses fragmented parallel processing, the verification often happens in under a second—comparable to or faster than traditional centralized database lookups, all while being significantly more secure.
What is the ROI of implementing the Trust Triad?
The ROI is measured in three ways:
- Fraud Prevention: Directly stopping million-dollar deepfake transfers.
- Efficiency: Reducing the time your SOC team spends on “false positives.”
- Compliance: Lowering insurance premiums and legal risks by eliminating biometric “honeypots.”
Conclusion: Engineering a Future of Invisible Trust
The “Trust Triad” represents a fundamental pivot in how you must think about security. We are leaving the era where you can trust what you see or hear. In its place, you must build a system where trust is earned through liveness, protected through decentralization, and enforced through autonomous agency.
By leveraging Agentic AI, Pindrop, and Anonybit, you are doing more than just stopping hackers; you are building a foundation of “Invisible Trust” that allows your business to move faster, innovate harder, and lead with confidence in the age of AI.
Don’t wait for the 3:00 AM alert that you can’t stop.
Call to Action
The window for “wait and see” has closed. If your enterprise is still relying on centralized biometrics and human-ear verification, you are one deepfake away from a crisis. Contact our security consultants today for a comprehensive audit of your identity stack and learn how the Trust Triad can be customized for your specific workflow. Let’s make your enterprise unhackable, together.